Explore the Zero Trust security model, its core principles, benefits, and challenges. Learn why Zero Trust is vital for modern cybersecurity.
What Is the Zero Trust Security Model?
The Zero Trust security model is a modern approach to cybersecurity that assumes no user or device, inside or outside the network, can be trusted by default. Instead, it requires strict identity verification and access controls for every user, device, and application trying to access resources.
Unlike traditional models, Zero Trust focuses on minimizing the risks of internal and external threats by using continuous authentication and monitoring. Security is not just about building a strong perimeter; it is about protecting every access point at all times. This model is especially relevant today as cloud computing, mobile devices, and remote work have changed how organizations operate and interact with data.
The Core Principles of Zero Trust
The foundation of Zero Trust is ‘never trust, always verify.’ This means every request for access is treated as if it comes from an open network. Security teams must verify identity, context, and compliance before granting access. For a detailed overview, see What is Zero Trust and how it works.
Zero Trust uses several key principles: least privilege access, segmentation, and continuous monitoring. Each step is designed to reduce the attack surface and limit potential damage from breaches. Least privilege means users and devices only get access to the resources they absolutely need. Segmentation divides the network into smaller zones, so if a breach happens, it is contained. Continuous monitoring uses tools and analytics to spot unusual behavior and act quickly.
Why Is Zero Trust Important Today?
Cyber threats have grown more sophisticated, and remote work has expanded the attack surface. Zero Trust addresses these challenges by verifying every user and device, regardless of location. This approach helps organizations protect sensitive data and operations from evolving threats.
Zero Trust is especially important in cloud environments, where users and devices can connect from anywhere. With more employees working remotely and using personal devices, the network edge is no longer clearly defined. Attackers often look for weak spots in remote connections, making strong identity and access controls essential.
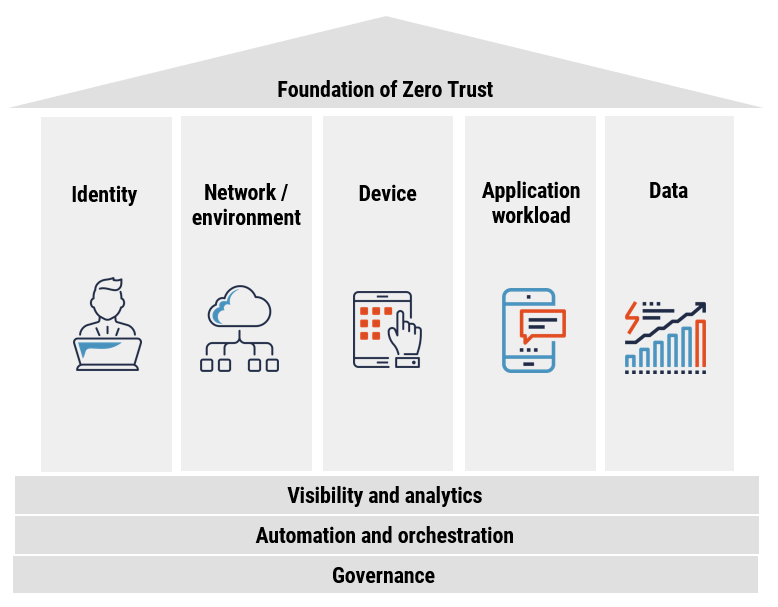
Key Components of Zero Trust Architecture
Zero Trust architecture includes several components: user authentication, device security, application security, and network segmentation. Multi-factor authentication (MFA) is commonly used to verify user identities. Network segmentation restricts access to sensitive areas, reducing risk if a breach occurs.
Strict access controls and continuous monitoring help detect unusual behavior and respond quickly. Organizations often use endpoint detection and response (EDR) tools to monitor devices and enforce policies. Device health checks are also important; only trusted, secure devices should access critical resources. Application security ensures that only approved apps can run in the environment, reducing risks from malware or unauthorized software.
Implementing Zero Trust in Your Organization
To adopt Zero Trust, organizations need to map their network, identify critical assets, and define strong access policies. Start by verifying user identities and devices, then apply least privilege access. Regularly review and update access permissions to maintain security.
The National Institute of Standards and Technology (NIST) offers guidelines on Zero Trust implementation.
Employee training is also important. Staff should understand the reasons behind Zero Trust and how to follow security protocols. A phased rollout helps organizations adjust gradually. Begin with high-risk areas and expand coverage over time. Integrating Zero Trust with existing security tools, such as firewalls and identity management platforms, can make the transition smoother. Regular audits and testing are key to maintaining a strong security posture.
Benefits of the Zero Trust Model
Zero Trust provides several benefits. It reduces the risk of data breaches by limiting access and quickly detecting threats. The model also helps organizations comply with regulations and protect sensitive information.
Zero Trust can improve visibility across the network, making it easier to spot suspicious activity. By applying the principle of least privilege, organizations reduce the impact of successful attacks. This approach also simplifies compliance with data protection laws, since access to sensitive data is tightly controlled and monitored. In addition, Zero Trust supports business agility by allowing secure remote access, which is essential for a modern workforce.
Challenges and Considerations
Adopting Zero Trust can be complex. Organizations may face challenges such as integrating new tools and updating legacy systems. It requires a cultural shift, as staff must adapt to stricter access controls and regular authentication.
Budget and resources can also be concerns. Planning and phased implementation help address these challenges. Leadership support is crucial for success. Some sectors, such as healthcare, face specific challenges due to regulatory requirements and the need to protect sensitive patient data. For an example of the importance of Zero Trust in healthcare, see this article from HealthIT.gov:.
Organizations must also consider the user experience. Too many security prompts can frustrate employees, so balancing security and usability is important. Automation and adaptive authentication help keep processes smooth while maintaining strong protection.
Zero Trust and the Future of Cybersecurity
Zero Trust is becoming a standard for organizations seeking strong security in a digital world. As threats evolve, this model helps prepare organizations for new challenges. Continuous improvement and adaptation will be key as technology and risks change.
For further reading, the Harvard Business Review discusses Zero Trust’s growing role in business security.
As more companies move to cloud-based infrastructure and adopt Internet of Things (IoT) devices, Zero Trust will play a crucial role in protecting data and operations. Automation, artificial intelligence, and machine learning will support Zero Trust by helping to identify threats faster and respond more effectively. The focus on identity, access, and continuous monitoring will remain central to future cybersecurity strategies.
How Zero Trust Relates to Compliance and Privacy
Compliance with data privacy laws is a major concern for many organizations. Zero Trust helps meet these requirements by ensuring that only authorized users can access sensitive data. Access is tracked and monitored, making it easier to demonstrate compliance during audits. Regulations like the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA) demand strict controls over who can see and use personal information.
Zero Trust also supports privacy by minimizing the amount of data each user can access. If a breach does occur, the amount of exposed data is limited, reducing potential harm to individuals and the organization. As privacy regulations become increasingly stringent worldwide, Zero Trust provides a strong framework for meeting these requirements.
Best Practices for a Successful Zero Trust Strategy
Start with a clear understanding of your organization’s assets and risks. Identify which data, applications, and systems are most critical. Apply the principle of least privilege everywhere, and use multi-factor authentication for all users. Regularly test and update security controls to keep up with new threats.
Engage all employees in the process. Provide training on recognizing phishing attempts, using secure passwords, and following access procedures. Use automation to enforce policies and reduce the risk of human error. Review access logs and monitor for unusual activity to catch problems early. By making Zero Trust part of your organization’s culture, you build a strong foundation for lasting security.
Conclusion
The Zero Trust security model is a significant step forward in protecting modern organizations from cyber threats. By requiring verification for every user and device, and applying strict access controls, Zero Trust helps reduce risks and limit the impact of breaches. As technology evolves, adopting this approach will be essential for strong cybersecurity. Organizations that embrace Zero Trust can better protect sensitive data, support remote work, and meet regulatory requirements. The journey may be challenging, but the benefits make it a worthwhile investment for the future.
FAQ
What does Zero Trust mean in cybersecurity?
Zero Trust is a security approach that assumes no user or device is trustworthy by default. Every access request must be verified, regardless of location.
How does Zero Trust differ from traditional security models?
Traditional models often trust users inside the network. Zero Trust requires verification for all users and devices, whether inside or outside.
Is Zero Trust only for large organizations?
No, organizations of all sizes can benefit from Zero Trust. The principles can be adapted to fit different needs and resources.
What are some challenges in implementing Zero Trust?
Challenges include integrating with legacy systems, managing costs, and changing organizational culture to support stricter access controls.
Does Zero Trust guarantee complete security?
No security model can guarantee complete protection, but Zero Trust reduces risks and helps organizations respond more effectively to threats.
How does Zero Trust support compliance with data privacy laws?
Zero Trust enforces strict access controls and auditing, making it easier to comply with regulations like GDPR and HIPAA by limiting and monitoring access to sensitive data.
What role does automation play in Zero Trust?
Automation helps enforce policies, monitor activity, and respond to threats quickly. It reduces the chance of human error and keeps security consistent across the organization.
Can Zero Trust be applied to legacy systems?
Yes, but it may require additional tools or updates. Organizations often phase in Zero Trust, starting with critical systems and gradually expanding coverage.
Visit our website for more.